Configure a machine to support ADFS and make sure you have access to the ADFS Management software. Address to your system administrator in this regard. Setup instructions can be added, following the steps in this online source will help to setup the ADFS env correctly https://www.virtuallyboring.com/how-to-setup-microsoft-active-directory-federation-services-adfs/
Configure ADFS to Recognize a New Orchestrator Instance
Note
The below steps are valid for the ADFS Management tool. Please note that the below procedure is a broad description of a sample configuration. For a fully detailed how-to, visit the official ADFS Documentation.
- Open ADFS Management and define a new relying party trust for Orchestrator as follows:
a. Click Relying Party Trusts.
b. In the Actions panel, click Add Relying Party Trust. The Add Relying Party Trust Wizard is displayed.
c. In the Welcome section, select Claims Aware.
d. In the Select Data section, choose the Enter data about relying party manually option.
e. In the Specify Display Name section, in the Display name field, insert the URL of the Orchestrator instance.
f. The Configure Certificate section does not need any specific settings so you may leave it as it is.
g. In the Configure URL section, select the Enable support for the SAML 2.0 Web SSO Protocol and fill in the URL of the Orchestrator instance plus the suffixidentity/Saml2/Acsin the Relying party SAML 2.0 SSO service URL field. For example,https://orchestratorURL/identity/Saml2/Acs.
h. In the Configure Identifiers section, fill in the URL of the Orchestrator instance plus the suffixidentity. For example,https://orchestratorURL/identity`. Make sure that the same format is displayed in (Actions > Properties > Identifiers).
i. In the Choose Access Control Policy section make sure to select the Permit everyone access control policy.
j. The next two sections (Ready to Add Trust and Finish) do not need any specific settings so you may leave them as they are.
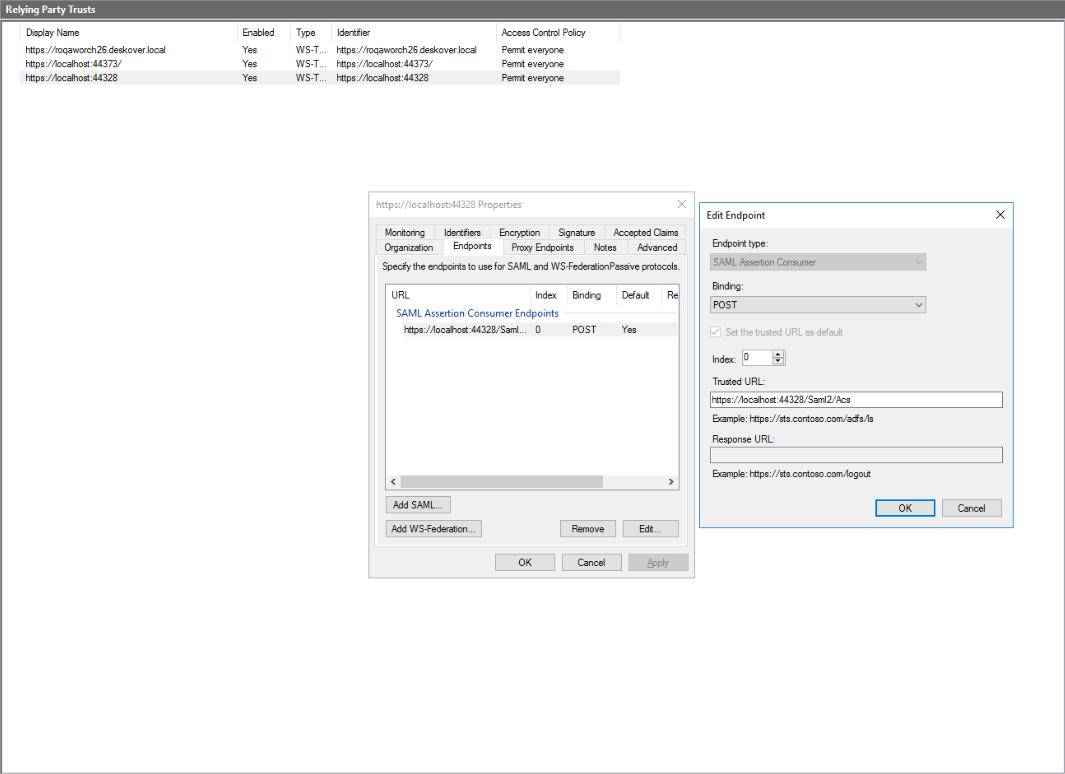
k. The newly added party trust is displayed on the Relying Party Trusts window.
l. Make sure that the default value for your URL is Yes (Actions > Properties > Endpoints).
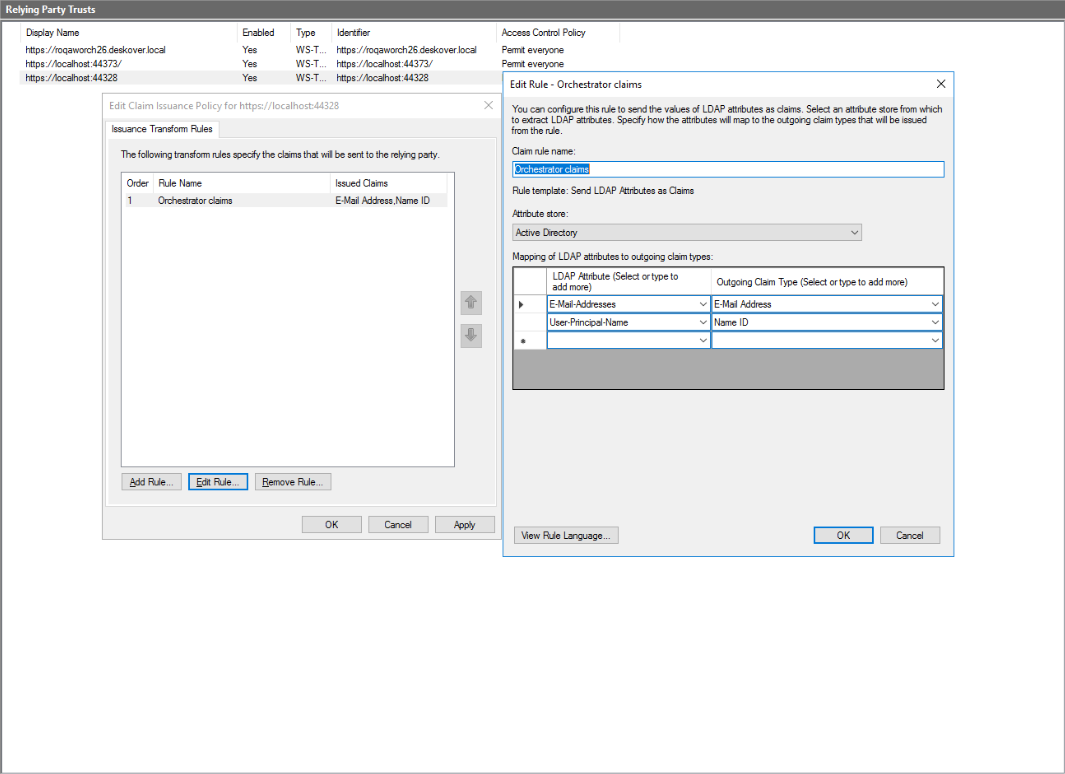
- Select the relying party trust and click Edit Claim Issuance Policy from the Actions panel. The Edit Claim Issuance Policy wizard is displayed.
- Click Add rule and create a new rule using the Send LDAP Attributes as Claims template with the following settings:
- In ADFS Management> Service> Certificates, right click to view CN=ADFS Signing certificate. Install Certificate, select Local Machine> Place all certificates in the following store. Import certificate to Personal and Trusted root certification authorities
- Once ADFS is configured, open PowerShell as an administrator and run the following commands:
Set-ADFSRelyingPartyTrust -TargetName "DISPLAYNAME" -SamlResponseSignature MessageAndAssertion(ReplaceDISPLAYNAMEwith the value set on point 1.e.)
Restart-Service ADFSSRV
If you want to verify the Identity Provider Entity ID
Go to https:///federationmetadata/2007-06/federationmetadata.xml
Set Orchestrator/Identity Server to Use ADFS Authentication
- Define a user in Orchestrator and have a valid email address set on the Users page.
- Import the signing certificate provided by the Identity Provider to the Windows certificate store using Microsoft Management Console. See here how to do that.
- Make sure that the following configuration is present in Identity Server's SAML2 settings within the External Providers page (read here how to access Identity Server):
- Select the Enabled check box.
- Set the Service Provider Entity ID parameter to
https://orchestratorURL/identity. - Set the Identity Provider Entity ID parameter to the value obtained by configuring ADFS authentication. For example,
http://<host name>/adfs/services/trustnotice s is missing from http - Set the Single Sign-On Service URL parameter to the value obtained by configuring ADFS authentication. For example,
http://<host name>/adfs/ls - Select the Allow unsolicited authentication response checkbox.
- Set the Return URL parameter to
https:/orchestratorURL/identity/externalidentity/saml2redirectcallback. - Set the External user mapping strategy parameter to
By user e-mail. - Set the SAML binding type parameter to
HTTP redirect. - In the Signing Certificate section, set Store name parameter to
Myfrom the drop-box. - Set the Store locationparameter to
LocalMachine. - Set the Thumbprint parameter to the thumbprint value of CN=ADFS Signing certificate provided in the Windows certificate store. Details here.
Note:
Replace all occurrences of
https://orchestratorURLwith the URL of your Orchestrator instance.Make sure that the URL of the Orchestrator instance does not contain a trailing slash. Always fill it in as
https:/orchestratorURL/identity, nothttps://orchestratorURL/identity/.
- Click Save to save the changes to the external identity provider settings.
- Restart the IIS server after performing any configuration changes within Identity Server.
- Go to admin (Built in user) add email address, add same user (email address) to your tenants.
- Launch the OR URL > Log in with user\domain.
Updated about a year ago