Configure OKTA to Recognize a New Orchestrator Instance
Note:
The below steps are valid for OKTA SAML setup. Please note that the below procedure is a broad description of a sample configuration. For a fully detailed how-to, visit the official OKTA Documentation.
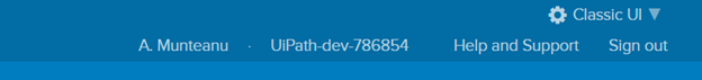
- Login to OKTA. The following setup is made in Classic UI view. You can change it from the drop-down on the top-right corner of the window.
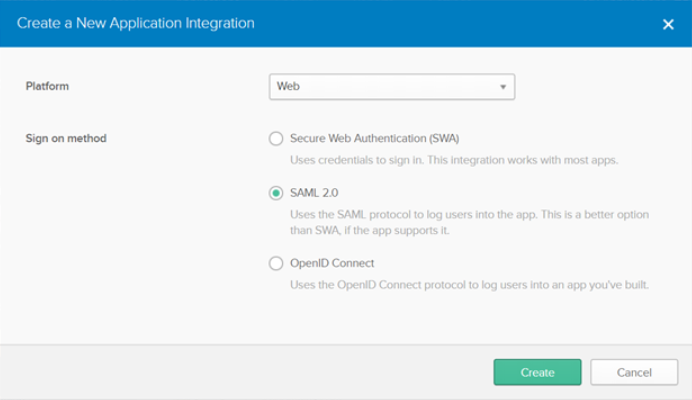
- On the Application tab, click Create New App. The Create a New Application Integration window is displayed.
- Choose SAML 2.0 as sign-on method and click Create.
- For the new integration, on the General Settings window, enter the application name.
- On the SAML Settings window, fill in the General section as per this example:
- Single sign on URL: The Orchestrator instance URL +
/identity/Saml2/Acs. For example,https://orchestratorURL/identity/Saml2/Acs. - Enable the Use this for Recipient URL and Destination URL check box.
- Audience URI:
https://orchestratorURL/identity - Name ID Format: EmailAddress
- Application Username: Email
- Single sign on URL: The Orchestrator instance URL +
Note
Whenever filling in the URL of the Orchestrator instance, make sure it does not contain a trailing slash. Always fill it in as
https://orchestratorURL/identity, nothttps://orchestratorURL/identity/.
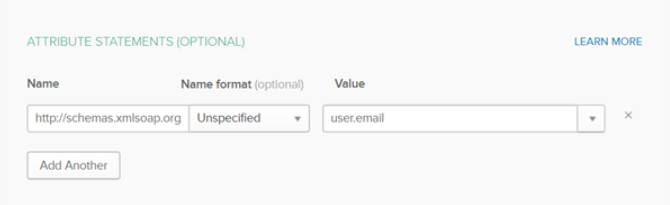
- Click Show Advanced Settings and fill in the Attribute Statements section:
- Set the Name field to
http://schemas.xmlsoap.org/ws/2005/05/identity/claims/emailaddressand select user.email from the Value drop-down.
- Set the Name field to
- Download the OKTA certificate.
- In the Feedback section, select the option that suits you and click Finish.
- On the Sign On tab, in the Settings section, click Setup Instructions. You are redirected to a new page containing the instructions required to complete your Orchestrator configuration for SAML 2.0: Identity Provider Sign-On URL, Identity Provider Issuer, X.509 Certificate.
Note
If, for any reason, the information about the identity provider is lost, you can, at any point, visit Sign On > Settings > View Setup Instructions.
Assigning People to the Application
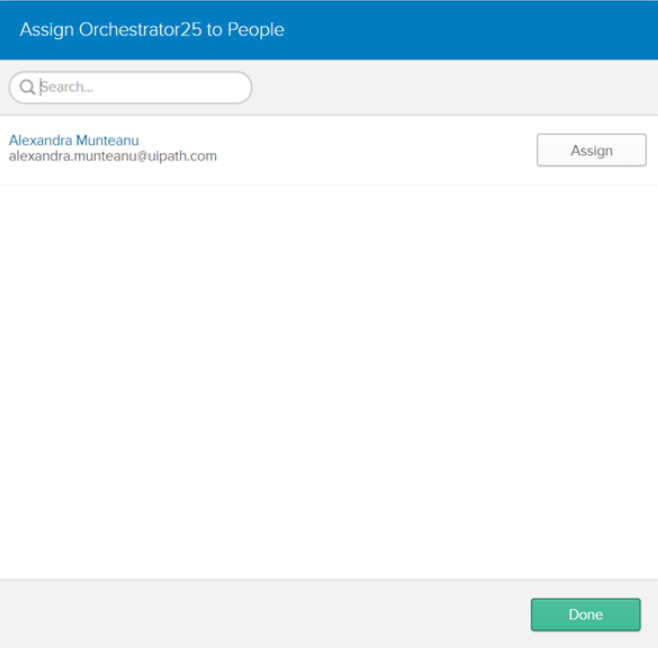
In order for a user to be able to use OKTA authentication, he must be assigned the newly created application:
- Login to OKTA.
- On the Application page, select the newly created application.
- On the Assignments tab, select Assign > Assign to People and then select the users to be given the necessary permissions.
- The newly added users are displayed on the People tab.
Set Orchestrator/Identity Server to Use OKTA Authentication
- Define a user in Orchestrator and have a valid email address set on the Users page.
- Import the signing certificate provided by the Identity Provider to the Windows certificate store using Microsoft Management Console. See step 9 in the Configure OKTA to Recognize a New Orchestrator Instance procedure.
- Make sure that the following configuration is present in Identity Server's Saml2 settings within External Providers page (read here how to access Identity Server):
- Select the Enabled check box.
- Set the Service Provider Entity ID parameter to
https://orchestratorURL/identity. - Set the Identity Provider Entity ID parameter to the value obtained by configuring OKTA authentication. See step 9 in the Configure OKTA to Recognize a New Orchestrator Instance procedure.
- Set the Single Sign-On Service URL parameter to the value obtained by configuring OKTA authentication. See step 9 in the Configure OKTA to Recognize a New Orchestrator Instance procedure.
- Select the Allow unsolicited authentication response check box.
- Set the Return URL parameter to
https://orchestratorURL/identity/externalidentity/saml2redirectcallback. Make sure to add/identity/externalidentity/saml2redirectcallbackat the end of the URL for the Return URL parameter. This path is specific to OKTA as it allows you to reach an Orchestrator environment directly from OKTA. - Set the SAML binding type parameter to
HTTP redirect. - In the Signing Certificate section, set Store name parameter to
Myfrom the drop-box. - Set the Store locationparameter to
LocalMachine. - Set the Thumbprint parameter to the thumbprint value provided in the Windows certificate store. Details here.
Note
Replace all occurrences of
https://orchestratorURLwith the URL of your Orchestrator instance.Make sure that the URL of the Orchestrator instance does not contain a trailing slash. Always fill it in as
https://orchestratorURL/identity, nothttps://orchestratorURL/identity/.
- Click Save to save the changes to the external identity provider settings.
- Restart the IIS server after performing any configuration changes within Identity Server.
Updated 2 years ago