Configure OKTA to Recognize a New Orchestrator Instance
Note:
The below steps are valid for OKTA SAML setup. Please note that the below procedure is a broad description of a sample configuration. For a fully detailed how-to, visit the official OKTA Documentation.
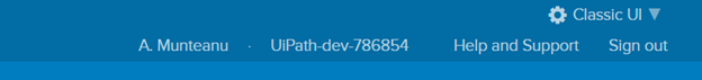
- Log in to OKTA. The following setup is made in Classic UI view. You can change it from the drop-down on the top-right corner of the window.
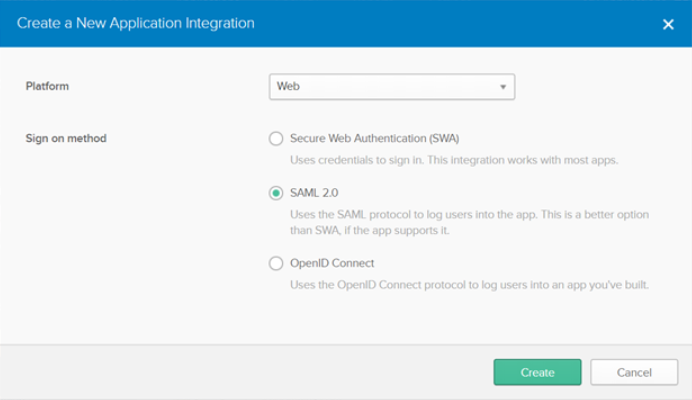
- On the Application tab, click Create New App. The Create a New Application Integration window is displayed.
- Choose SAML 2.0 as sign-on method and click Create.
- For the new integration, on the General Settings window, enter the application name.
- On the SAML Settings window, fill in the General section as per this example:
- Single sign on URL: The Orchestrator instance URL +
/identity/Saml2/Acs. For example,https://myOrchestrator.uipath.com/identity/Saml2/Acs. - Enable the Use this for Recipient URL and Destination URL check box.
- Audience URI:
https://myOrchestrator.uipath.com/identity - Name ID Format: EmailAddress
- Application Username: Email
- Single sign on URL: The Orchestrator instance URL +
Note
Whenever filling in the URL of the Orchestrator instance, make sure it does not contain a trailing slash. Always fill it in as
https://myOrchestrator.uipath.com/identity, nothttps://myOrchestrator.uipath.com/identity/.
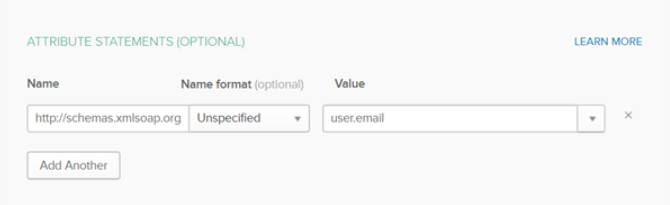
- Click Show Advanced Settings and fill in the Attribute Statements section:
- Set the Name field to
http://schemas.xmlsoap.org/ws/2005/05/identity/claims/emailaddressand select user.email from the Value drop-down.
- Set the Name field to
- Download the OKTA certificate.
- In the Feedback section, select the option that suits you and click Finish.
- On the Sign On tab, in the Settings section, click Setup Instructions. You are redirected to a new page containing the instructions required to complete your Orchestrator configuration for SAML 2.0: Identity Provider Sign-On URL, Identity Provider Issuer, X.509 Certificate.
Note
If, for any reason, the information about the identity provider is lost, you can, at any point, visit Sign On > Settings > View Setup Instructions.
Assigning People to the Application
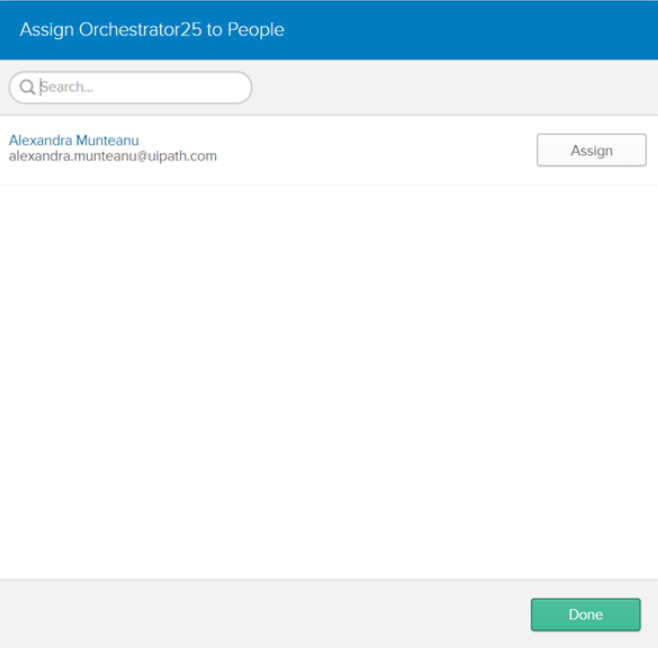
In order for a user to be able to use OKTA authentication, he must be assigned the newly created application:
- Log in to OKTA.
- On the Application page, select the newly created application.
- On the Assignments tab, select Assign > Assign to People and then select the users to be given the necessary permissions.
- The newly added users are displayed on the People tab.
Set Orchestrator/Identity Server to Use OKTA Authentication
- Define a user in Orchestrator and have a valid email address set on the Users page.
- Import the signing certificate.
- For Windows deployments, import the signing certificate provided by the Identity Provider to the Windows certificate stores (Trusted Root Certification Authorities and Personal stores) using Microsoft Management Console.
- For Azure deployments, upload the certificate provided by the Identity Provider From in the Azure portal. (TLS/SSL settings > Public Certificates (.cer) > Upload Public Key Certificate). See here how to adjust your web app configuration if you are unable to use OKTA authentication and encounter the following error message:
An error occurred while loading the external identity provider. Please check the external identity provider configuration.
- Make sure that the following configuration is present in Identity Server's Saml2 settings within External Providers page (read here how to access Identity Server).
Note
Replace all occurrences of
https://myOrchestrator.uipath.com/identitywith the URL of your Orchestrator instance.Make sure that the URL of the Orchestrator instance does not contain a trailing slash. Always fill it in as
https://myOrchestrator.uipath.com/identity, nothttps://myOrchestrator.uipath.com/identity/.
General Steps
| Step | Field | Value |
|---|---|---|
| 4. | Enabled checkbox | Must be enabled. |
| 5. | Service Provider Entity ID | Set to https://myOrchestrator.uipath.com/identity. |
| 6. | Identity Provider Entity ID | Set to the value obtained by configuring OKTA authentication. See step 9 in the Configure OKTA to Recognize a New Orchestrator Instance procedure. |
| 7. | Allow unsolicited authentication response checkbox | Must be enabled. |
| 8. | Return URL | Set to https://myOrchestrator.uipath.com/identity/externalidentity/saml2redirectcallback. Make sure to add /identity/externalidentity/saml2redirectcallback at the end of the URL for the Return URL parameter. This path is specific to OKTA as it allows you to reach an Orchestrator environment directly from OKTA. |
| 9. | SAML binding type | Set to HTTP redirect. |
Signing Certificate Steps
Ensure the certificate is installed in the Trusted Root Certification Authorities and Personal certificate stores.
Learn how to configure Orchestrator/Identity Server to use a private key certificate.
| Step | Field | Value |
|---|---|---|
| 10. | Store name | Set to My from the drop-box. |
| 11. | Store location | Set to LocalMachine for Windows deployments.Set to CurrentUser for Azure Web App deployments. |
| 12. | Thumbprint | Set to the thumbprint value provided in the Windows certificate store. |
Service Certificate Steps
Optional. Required to encrypt SAML assertions if you configured Identity Server not to use SSL (e.g., SSL offloading in load-balanced environments). The external identity provider encrypts SAML assertions using the public key of the service certificate, and Identity Server decrypts them with the certificate's private key.
Important
The service certificate needs to:
- have a public key on 2048 bits
- have a private key accessible by the AppPool user,
- be in its validity period (not expired).
| Step | Field | Value |
|---|---|---|
| 13. | Store name | Set to My from the drop-box. |
| 14. | Store location | Set to LocalMachine. |
| 15. | Thumbprint | Set to the thumbprint value provided in the Windows certificate store. Details here. |
- Click Save to save the changes to the external identity provider settings.
- Restart the IIS server after performing any configuration changes within Identity Server.
Updated 2 years ago